I came to conclusion that dealing with certificates might be a challenge, especially when You are forced to do that occasionally and just want to get stuff done.
In this blog post, I'm going to show how to create and consume a certificate in .NET Core. Should be easy as pie.
Create/Install
Let's launch this PowerShell script to create a certificate and install it to the Trusted Roots:
$cert = New-SelfSignedCertificate -Subject localhost -DnsName localhost -FriendlyName ".NET Core dev certificate" -KeyUsage DigitalSignature -TextExtension @("2.5.29.37={text}1.3.6.1.5.5.7.3.1")
Export-Certificate -Cert $cert -FilePath dotnet.core.dev.cer
Import-Certificate -FilePath dotnet.core.dev.cer -CertStoreLocation cert:/CurrentUser/Root
Consume
1.IIS
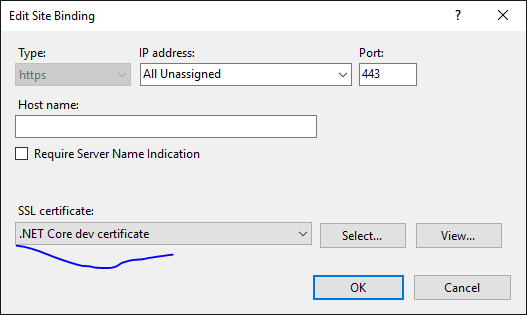
Starting from this You will be able to consume it in IIS (if it is Your reverse proxy of choice for .NET Core apps). Just go ahead and edit bindings for Your site:
2.Kestrel
First of all install Microsoft.AspNetCore.Server.Kestrel.Https package:
dotnet add package Microsoft.AspNetCore.Server.Kestrel.Https
Then leverage Kestrel's options by providing certificate created above, to tune HTTPS stuff:
var host = new WebHostBuilder()
.UseKestrel(options => {
var cr = new X509Certificate2("./Certificates/dotnet.core.dev.cer");
options.UseHttps(cr);
})
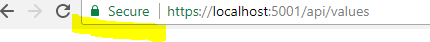
Btw. Chrome feels happy with that configuration and the certificate is displayed as green:
Just in case here is a link to that demo in my GitHub. Enjoy.